The computational complexity of universal hashing | Proceedings of the twenty-second annual ACM symposium on Theory of Computing
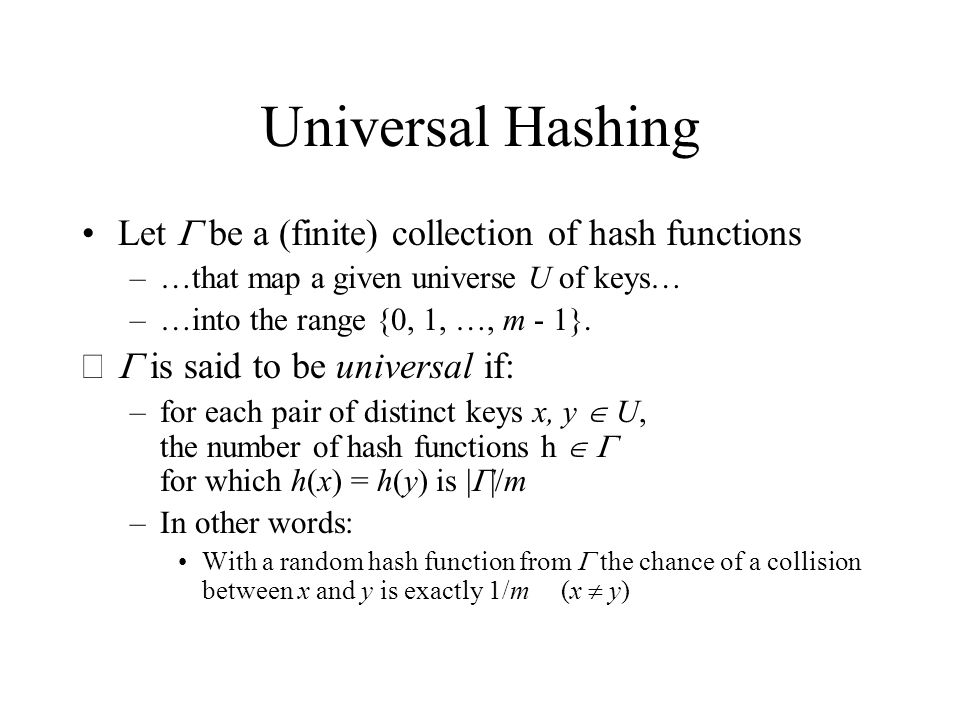
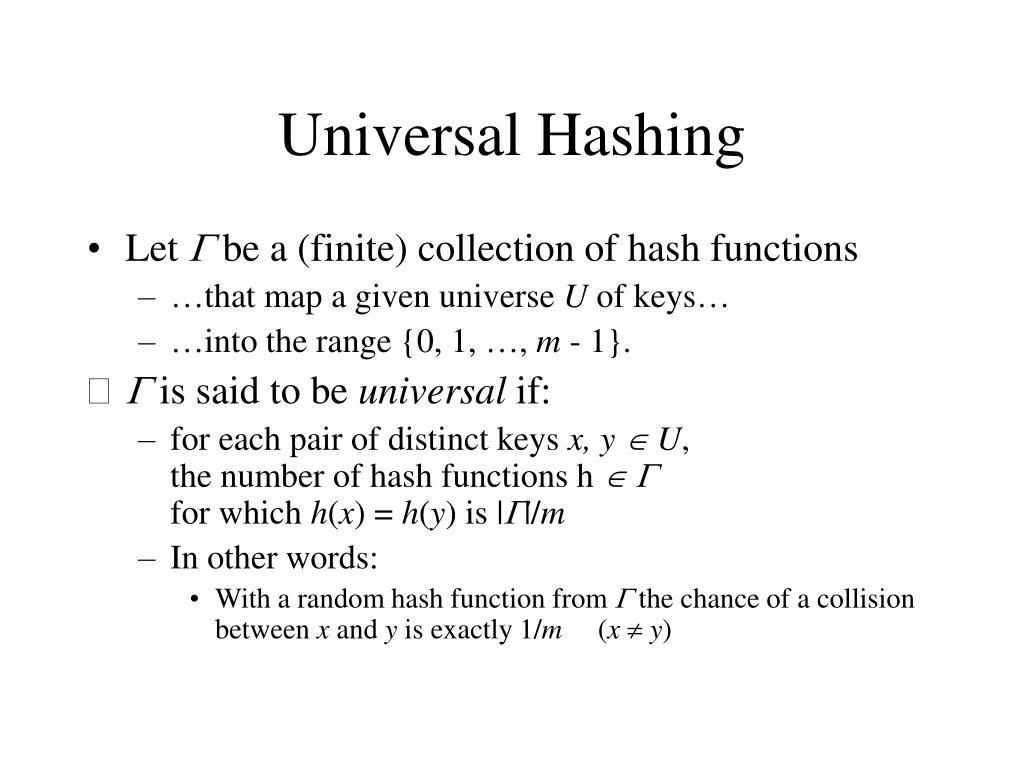
Universal Hashing When attempting to foil an malicious adversary, randomize the algorithm Universal hashing: pick a hash function randomly when the algorithm. - ppt download
![PDF] Tabulation based 4-universal hashing with applications to second moment estimation | Semantic Scholar PDF] Tabulation based 4-universal hashing with applications to second moment estimation | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/5f8b99892f73b2ccefeaed5aa6cb36b7afcb4d33/9-Table1-1.png)